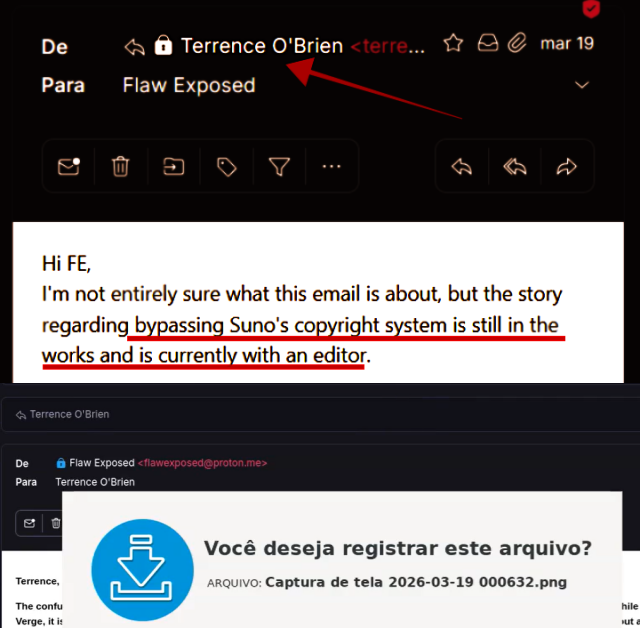
After being ignored by the world press for trying to denounce this crime, I've made the archives publicly available for anyone who's interested. I'm not exposing myself—this is irrefutable evidence. Anyone can use the archives; I'm not asking to be credited or paid—I only want this truth to be made public. And don't forget: the press is complicit.
The document is a Certified Report of Technical Digital Content Capture (Identifier: 69bc-0cec-6336-2411), issued in compliance with international computer forensics standards (ISO 27037) and the principles of the chain of custody of the Brazilian Criminal Procedure Code.
- The material has an ICP-Brazil digital signature and a National Observatory Timestamp, guaranteeing public faith, absolute integrity, and impossibility of tampering.
- The corresponding network metadata packages, source code, and HTTP requests are consolidated in the attached file capture_69bc0cec63362411.zip (HASH SHA512 protected in the report).
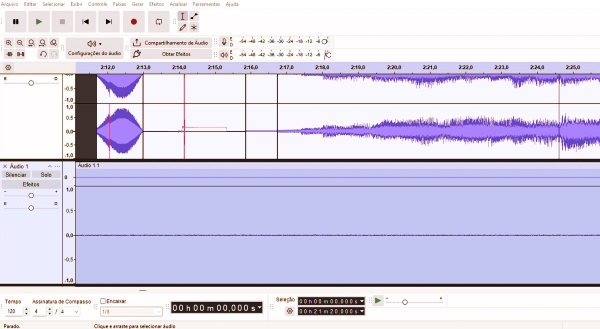
In the hyper-accelerated era of generative AI, the concept of "truth" has become a moving target. We are living through the death of the simple screenshot; in a world where deepfakes and AI-generated music can be conjured and deleted in seconds, a static image is a ghost—easily manipulated and legally fragile. To bridge the gap between a "he-said-she-said" dispute and the forensic certainty required by a court of law, we are witnessing the rise of "technical capture." This isn't just about recording a screen; it’s about a new standard of digital trust where the platform itself serves as an immutable witness to the velocity of online events
- Cryptographic Signatures: The capture package is anchored by HASH SHA512 and SHA3-512 signatures. This is a digital fingerprint; if a single byte of the captured Suno generation were altered, the HASH would break, alerting the court to tampering
- Network Provenance: The report tracked the specific IP address ***.100.62.204, providing a geographical and technical anchor for the session..
- Navigation Continuity: The logs show a seamless transition from Suno.com to Google OAuth for authentication. This proves the use.
- ICP-Brasil Certification: The final report is sealed using signatures managed by the Brazilian National Institute of Information Technology, ensuring the document carries the full weight of federal authentication.
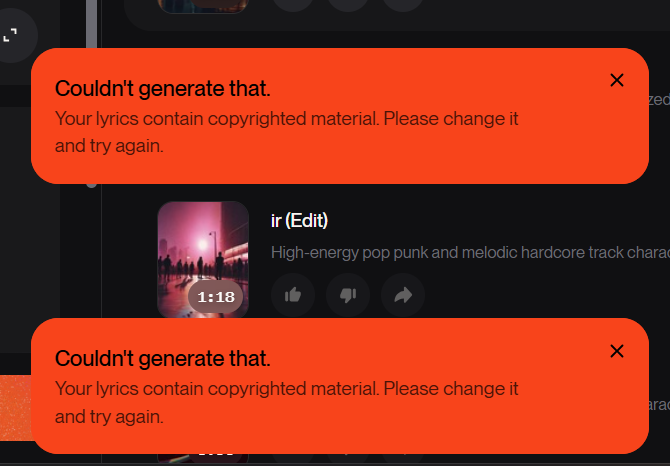
AI music cloning and copyright litigation
*Under Article 369 of the CPC, Verifact constitutes a "legal and morally legitimate means" to demonstrate facts. More importantly, when combined with MP nº 2.200-2/2001, the use of ICP-Brasil Digital Certificates grants the report a legal presumption of integrity and anteriority.